About configuring default setup at scale
With default setup for code scanning, you can quickly secure code in repositories across your organization.
You can enable code scanning for all repositories in your organization that are eligible for default setup. After enabling default setup, the code written in CodeQL-supported languages in repositories in the organization will be scanned:
- On each push to the repository's default branch, or any protected branch. For more information on protected branches, see "About protected branches."
- When creating or committing to a pull request based against the repository's default branch, or any protected branch, excluding pull requests from forks.
- On a weekly schedule.
For more information, see "Configuring default setup for all eligible repositories in an organization."
You can also use security overview to find a set of repositories in your organization and enable or disable default setup for all of them at the same time. For more information, see "Configuring default setup for a subset of repositories in an organization."
You can also create different default setup configurations for individual repositories. For more information on configuring default setup at the repository level, see "Configuring default setup for code scanning."
For repositories that are not eligible for default setup, you can configure advanced setup at the repository level, or at the organization level using a script. For more information, see "Configuring advanced setup for code scanning with CodeQL at scale."
Eligible repositories for CodeQL default setup at scale
A repository must meet all the following criteria to be eligible for default setup, otherwise you need to use advanced setup.
- Advanced setup for code scanning is not already enabled.
- GitHub Actions are enabled.
- Publicly visible, or GitHub Advanced Security is enabled.
We recommend enabling default setup for eligible repositories if there is any chance the repositories will include at least one CodeQL-supported language in the future. If you enable default setup on a repository that does not include any CodeQL-supported languages, default setup will not run any scans or use any GitHub Actions minutes. If CodeQL-supported languages are added to the repository, default setup will automatically begin scanning CodeQL-supported languages and using GitHub Actions minutes. For more information on CodeQL-supported languages, see "About code scanning with CodeQL."
Note
Configuring default setup for all repositories in an organization through your organization's settings page will not override existing configurations of default setup. However, configuring default setup on a subset of repositories in an organization through security overview will override existing configurations of default setup on those repositories.
About adding languages to an existing default setup configuration
If the code in a repository changes to include a CodeQL-supported language, GitHub will automatically update the code scanning configuration to include the new language. If code scanning fails with the new configuration, GitHub will resume the previous configuration automatically so the repository does not lose code scanning coverage.
Configuring default setup for all eligible repositories in an organization
You can enable default setup for all eligible repositories in your organization. For more information, see "About enabling security features at scale."
Extending CodeQL coverage in default setup
Through your organization's security settings page, you can extend coverage in default setup using model packs for all eligible repositories in your organization. For more information, see "Editing your configuration of default setup."
Configuring default setup for a subset of repositories in an organization
You can filter for specific repositories you would like to configure default setup for. For more information, see "Applying a custom security configuration."
Through security overview for your organization, you can find eligible repositories for default setup, then enable default setup across each of those repositories simultaneously. For more information on repository eligibility, see "Eligible repositories for CodeQL default setup at scale."
Finding repositories that are eligible for default setup
-
On GitHub, navigate to the main page of the organization.
-
Under your organization name, click Security.
-
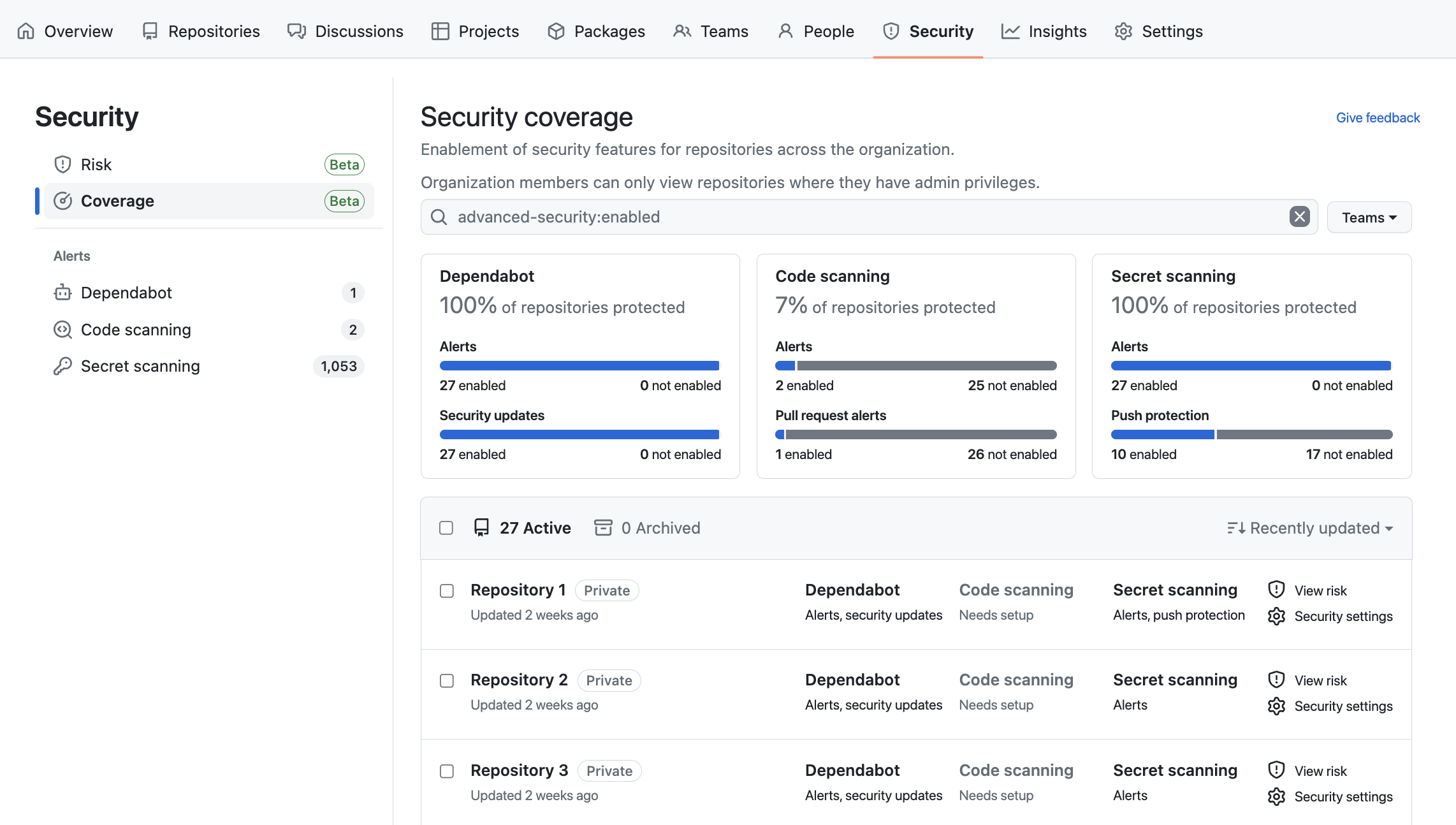
In the sidebar, click Coverage to display the "Security coverage" view.
-
In the search bar, enter one of the following queries:
code-scanning-default-setup:eligible is:publicshows repositories that are eligible for default setup because they are visible to the public and have GitHub Actions enabled.code-scanning-default-setup:eligible advanced-security:enabledshows private or internal repositories that are eligible for default setup because they have both GitHub Advanced Security and GitHub Actions enabled.code-scanning-default-setup:not-eligibleshows repositories that are ineligible for default setup enablement at scale for any of the following reasons:- The repositories already have existing configurations of advanced setup.
- The repositories do not have GitHub Actions enabled.
- The repositories are private or internal and do not have GitHub Advanced Security enabled.
Configuring merge protection for all repositories in an organization
You can use rulesets to prevent pull requests from being merged when one of the following conditions is met:
-
A required tool found a code scanning alert of a severity that is defined in a ruleset.
-
A required code scanning tool's analysis is still in progress.
-
A required code scanning tool is not configured for the repository.
For more information, see "Set code scanning merge protection." For more general information about rulesets, see "About rulesets."