About custom auto-triage rules
You can create your own Dependabot auto-triage rules based on alert metadata. You can choose to auto-dismiss alerts indefinitely, or snooze alerts until a patch becomes available, and you can specify which alerts you want Dependabot to open pull requests for.
Since any rules that you create apply to both future and current alerts, you can also use auto-triage rules to manage your Dependabot alerts in bulk.
Repository administrators can create custom auto-triage rules for their public repositories.
Organization owners and security managers can set custom auto-triage rules at the organization-level, and then choose if a rule is enforced or enabled across all public repositories in the organization.
- Enforced: If an organization-level rule is "enforced", repository administrators cannot edit, disable, or delete the rule.
- Enabled: If an organization-level rule is "enabled", repository administrators can still disable the rule for their repository.
Note
In the event that an organization-level rule and a repository-level rule specify conflicting behaviors, the action set out by the organization-level rule takes precedence. Dismissal rules always act before rules which trigger Dependabot pull requests.
You can create rules to target alerts using the following metadata:
- CVE ID
- CWE
- Dependency scope (
devDependencyorruntime) - Ecosystem
- GHSA ID
- Manifest path (for repository-level rules only)
- Package name
- Patch availability
- Severity
Understanding how custom auto-triage rules and Dependabot security updates interact
You can use custom auto-triage rules to tailor which alerts you want Dependabot to open pull requests for. However, for an "open a pull request" rule to take effect, you must ensure that Dependabot security updates are disabled for the repository (or repositories) that the rule should apply to.
When Dependabot security updates are enabled for a repository, Dependabot will automatically try to open pull requests to resolve every open Dependabot alert that has an available patch. If you prefer to customize this behavior using a rule, you must leave Dependabot security updates disabled.
For more information about enabling or disabling Dependabot security updates for a repository, see "Configuring Dependabot security updates."
Adding custom auto-triage rules to your repository
Note
During the public preview, you can create up to 10 custom auto-triage rules for a repository.
-
On GitHub, navigate to the main page of the repository.
-
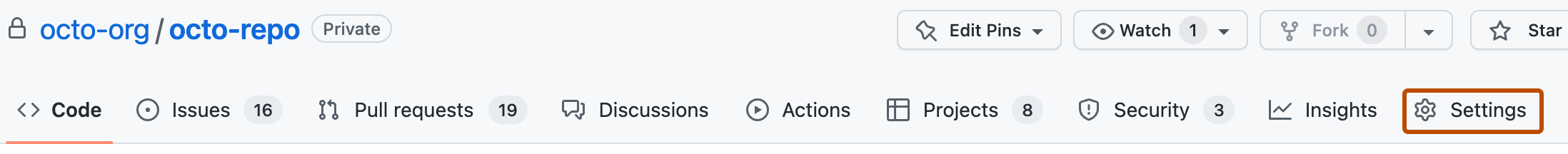
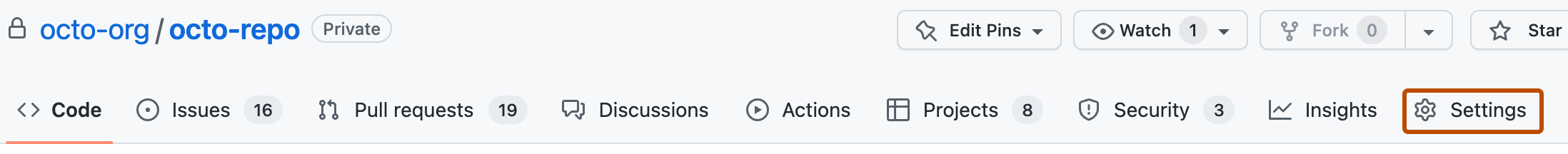
Under your repository name, click Settings. If you cannot see the "Settings" tab, select the dropdown menu, then click Settings.
-
In the "Security" section of the sidebar, click Code security and analysis.
-
Under "Dependabot alerts", click close to "Dependabot rules".
-
Click New rule.
-
Under "Rule name", describe what this rule will do.
-
Under "State", use the dropdown menu to select whether the rule should be enabled or disabled for the repository.
-
Under "Target alerts", select the metadata you want to use to filter alerts.
-
Under "Rules", select the action you want to take on alerts that match the metadata:
- Select Dismiss alerts to auto-dismiss alerts that match the metadata. You can choose to dismiss alerts indefinitely or until a patch is available.
- Select Open a pull request to resolve this alert if you want Dependabot to suggest changes to resolve alerts that match the targeted metadata. Note that this option is unavailable if you have already selected the option to dismiss alerts indefinitely, or if Dependabot security updates are enabled in your repository settings.
-
Click Create rule.
Adding custom auto-triage rules to your organization
You can add custom auto-triage rules for all eligible repositories in your organization. For more information, see "Configuring global security settings for your organization."
Editing or deleting custom auto-triage rules for your repository
-
On GitHub, navigate to the main page of the repository.
-
Under your repository name, click Settings. If you cannot see the "Settings" tab, select the dropdown menu, then click Settings.
-
In the "Security" section of the sidebar, click Code security and analysis.
-
Under "Dependabot alerts", click close to "Dependabot rules".
-
Under "Repository rules", to the right of the rule that you want to edit or delete, click .
-
To edit the rule, make any changes to the applicable fields, then click Save rule.
-
To delete the rule, under "Danger Zone", click Delete rule.
-
In the "Are you sure you want to delete this rule?" dialog box, review the information, then click Delete rule.
Editing or deleting custom auto-triage rules for your organization
You can edit or delete custom auto-triage rules for all eligible repositories in your organization. For more information, see "Configuring global security settings for your organization."